- Print
- DarkLight
- PDF
Configure Data Loss Prevention Policies (DLP) for HTTP Connectors
- Print
- DarkLight
- PDF
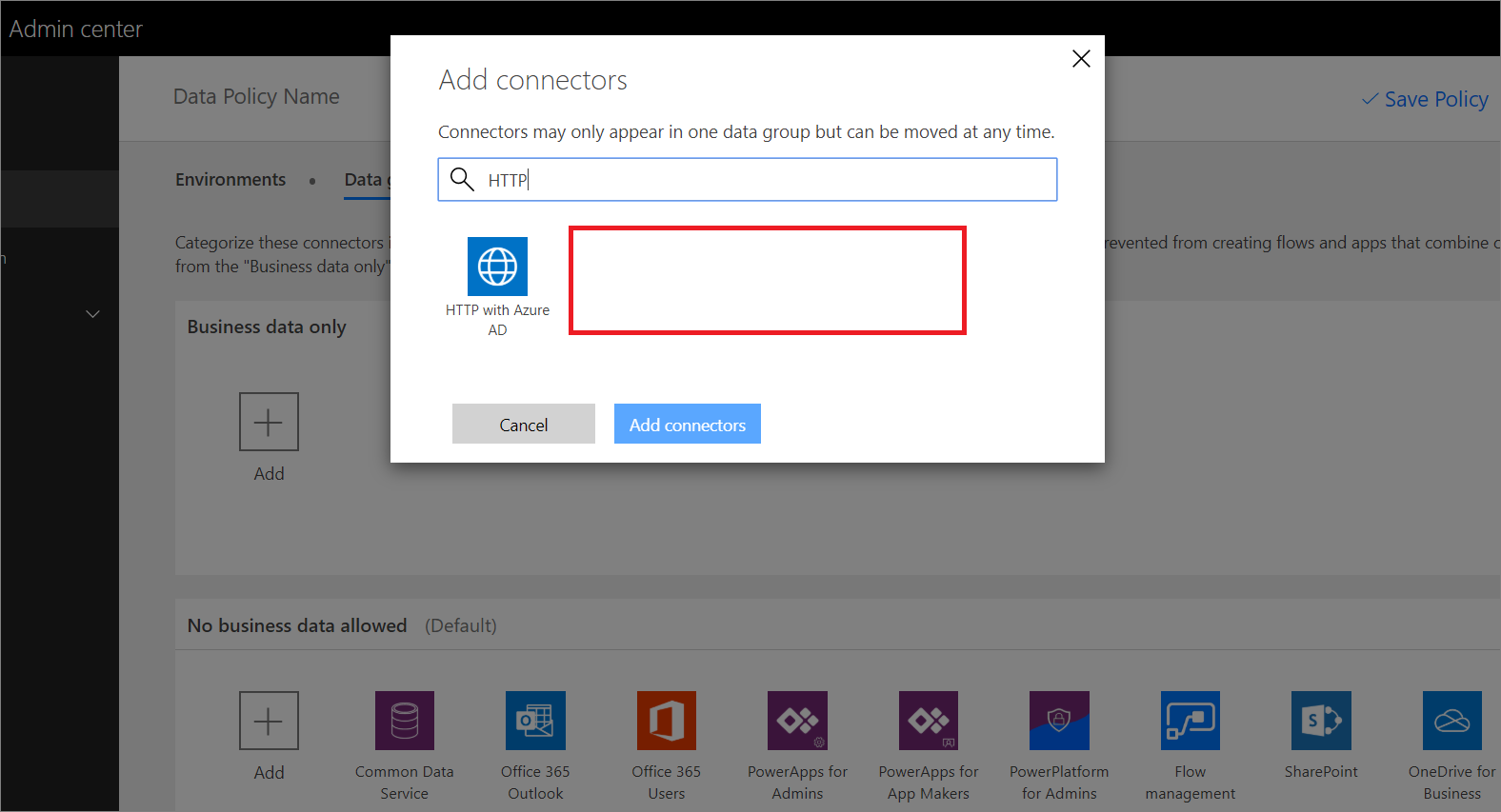
If you look closely at the DLP Policy editor, in the Power Automate Admin center, you will discover HTTP connectors do not show up in the list of connectors that can be managed by DLP Policies. The only related HTTP connector that shows up is the HTTP with Azure AD connector.
For many administrators, this causes some concerns as someone can use an HTTP connector to send information to destinations that are not endorsed by your organization.
However, there is a solution that exists outside of the DLP editor. Administrators can use the Power Apps and Power Automate Powershell Cmdlets when creating DLP policies that include an updated SchemaVersion; which allows administrators to create policies that include HTTP Connectors.
After installing the Powershell modules, an Administrator can issue the following command that will create a new policy that includes HTTP connector support:
New-AdminDlpPolicy -DisplayName "HTTP DLP Policy" -SchemaVersion 2018-11-01
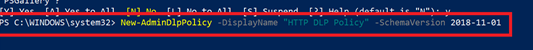
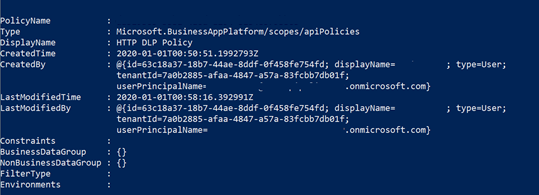
After the command is issued, a response will be returned indicating that the DLP policy has been successfully created.
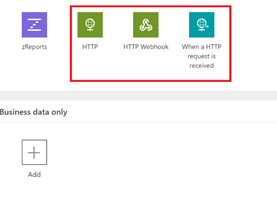
If we now head back to the Power Automate Admin center, we will now discover that we have the HTTP, HTTP Webhook and When a HTTP request is received connectors available to be managed in DLP policies.
Conclusion
Preventing data leakage in your organization is an important activity for administrators. In order to prevent incidental business data leakage, administrators should be creating DLP policies that include HTTP connectors. For now, that means using the Powershell cmdlets when creating new DLP policies.

