- Print
- DarkLight
- PDF
Detect changes in your Azure Subscriptions or Resource Groups with Azure Event Grid
- Print
- DarkLight
- PDF
With Azure Event Grid you can centrally manage your events by routing events to various handlers through subscriptions with filters (see also tip Advanced Filtering). Events emit from either a custom event source (custom Event Topic) or several supported Azure services such as Service Bus, Storage, Azure Resource Groups (subscription).
Within an Azure subscription, you can create event handlers for events occurring in a resource group level (Microsoft.Resources.ResourceGroups) or subscription level (Microsoft.Resources.Subscriptions). The events are listed below:
| Event type | Description |
|---|---|
| Microsoft.Resources.ResourceActionCancel | Raised when action on a resource is cancelled. |
| Microsoft.Resources.ResourceActionFailure | Raised when action on resource fails. |
| Microsoft.Resources.ResourceActionSuccess | Raised when action on resource succeeds. |
| Microsoft.Resources.ResourceDeleteCancel | Raised when a delete operation is cancelled. This event happens when a template deployment is cancelled. |
| Microsoft.Resources.ResourceDeleteFailure | Raised when delete operation fails. |
| Microsoft.Resources.ResourceDeleteSuccess | Raised when delete operation succeeds. |
| Microsoft.Resources.ResourceWriteCancel | Raised when create or update operation is cancelled. |
| Microsoft.Resources.ResourceWriteFailure | Raised when create or update operation fails. |
| Microsoft.Resources.ResourceWriteSuccess | Raised when create or update operation succeeds. |
Source: https://docs.microsoft.com/en-us/azure/event-grid/event-schema-resource-groups#available-event-types
The above events are raised on any PUT, PATCH, POST, and DELETE operations that are sent to management.azure.com. For instance, when you create an Azure resource and the operation succeeds the Microsoft.Resources.ResourceActionSuccess event will be emitted and potentially handled when an event handler subscribes to it.
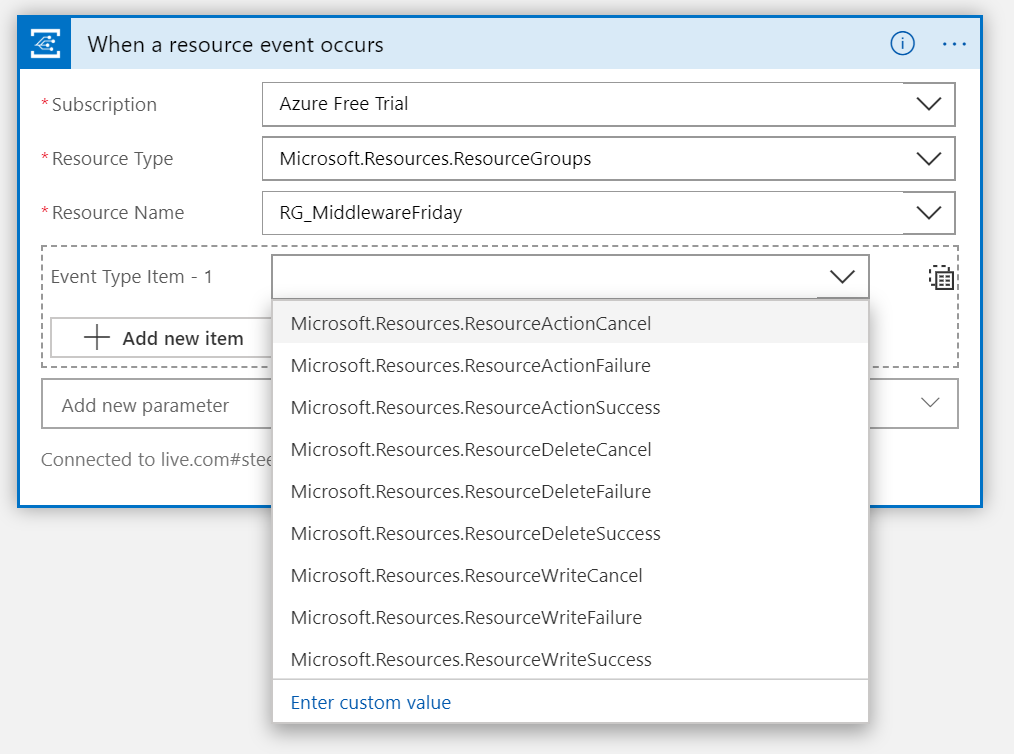
You can create a Logic App with an Event Grid trigger and decide whether you like to subscribe to events on the resource group level:
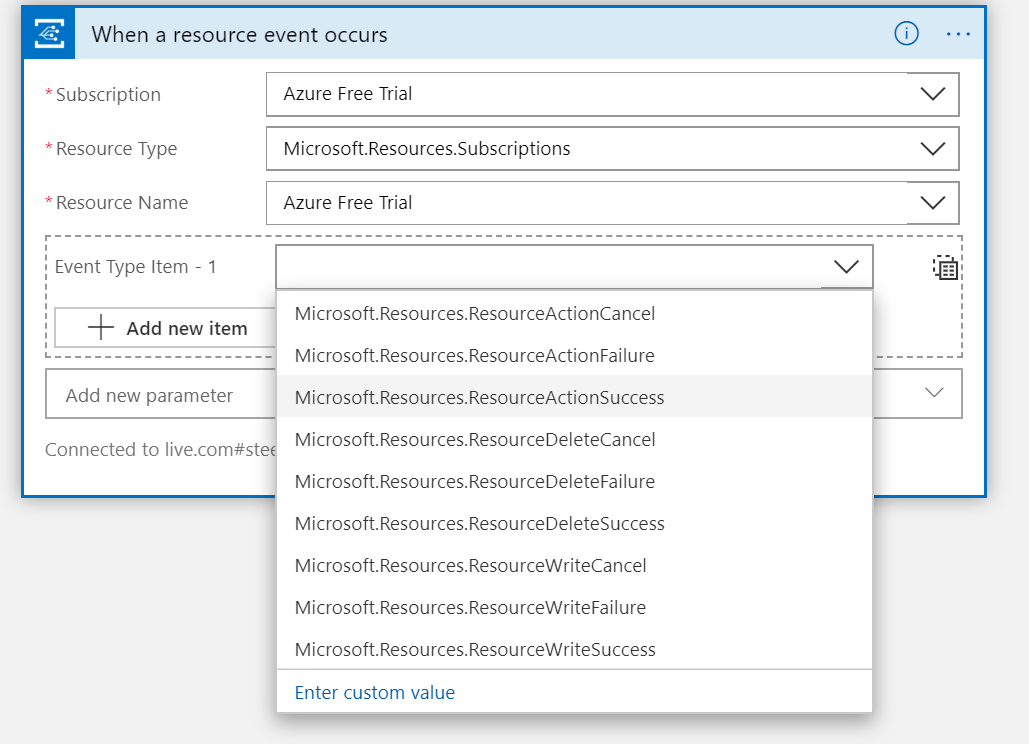
Or subscription level:
In both cases, you handle the event in a Logic App. You can create an Azure automation job deleting the resource when the Azure resource resides in a region not allowed by IT policies.


