Managed Identity Authentication
- Print
- DarkLight
- PDF
Managed Identity Authentication
- Print
- DarkLight
- PDF
Article summary
Did you find this summary helpful?
Thank you for your feedback!
This article explains how to create an Azure Active Directory (AD) managed identity for an Azure API Management instance and how to securely access other Azure AD-protected resources, such as Azure Function App. Using Azure AD manages this identity, so you don't have to pass passwords between resources or rotate secrets.
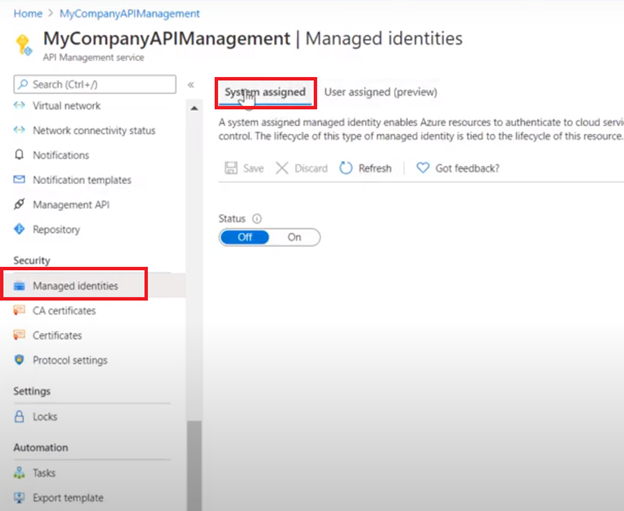
- Go to your API Management Instance -> Managed Identities -> System Assigned (as shown in the screenshot).
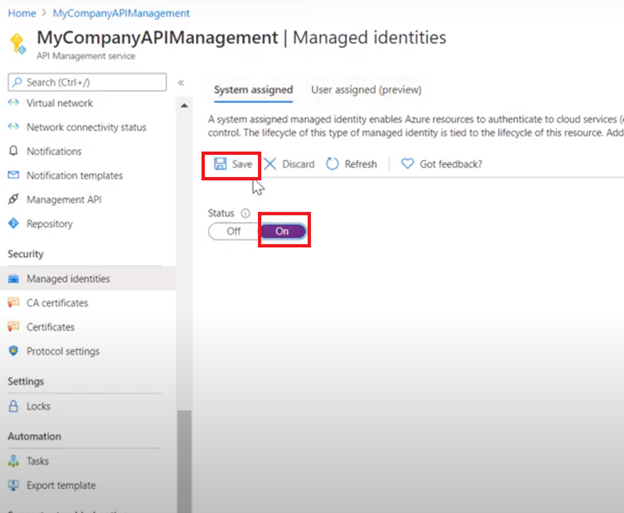
- Turn the Status “On” and then save your changes.
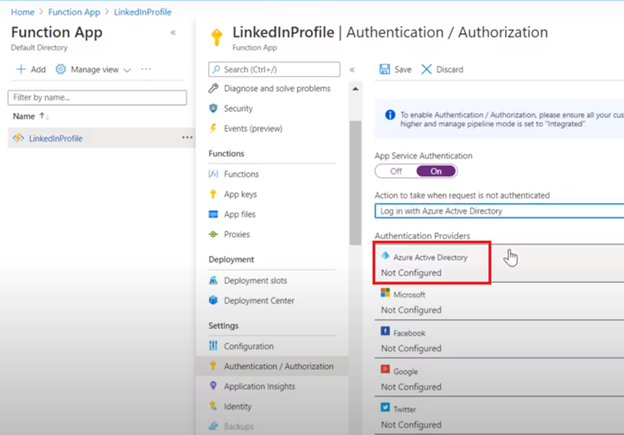
- Then, browse the Azure resource you want to set the Managed Identity Authentication with the API Management. In this case, our resource is an Azure Function App. Then browse to “Authentication & Authorization” as shown in the figure.
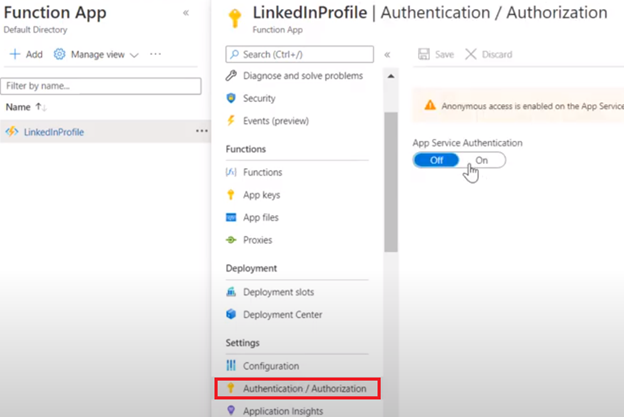
- Turn “App Service Authentication” On.
- Open “Action to take when the request is not authenticated” dropdown, and select “Login with Azure Active Directory” as shown in the picture below:
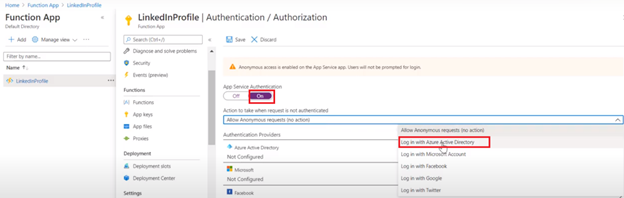
- In the Authentication Providers, select “Azure Active Directory”, and you should find it as “not configured” as shown in the picture.
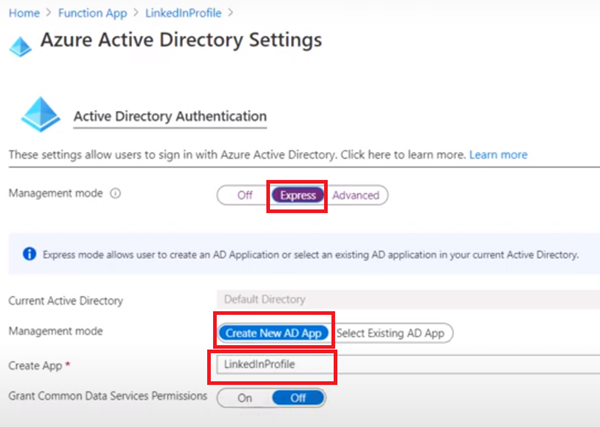
- Select “Express” Management Mode, then "Create New AD App” from the second Management Mode. Then add a name for your App as shown in the picture below:
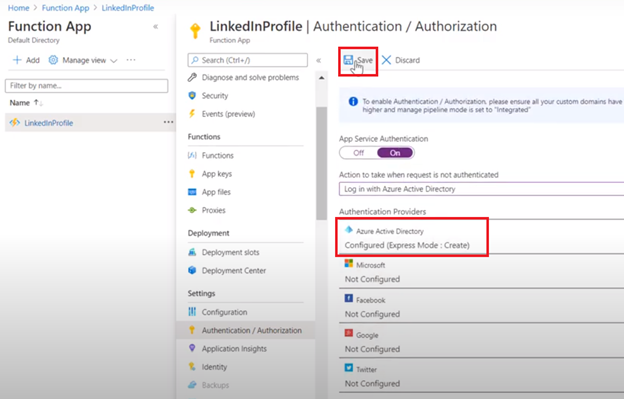
- Go ahead and save your changes.
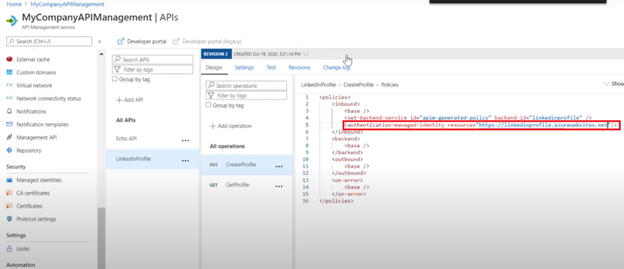
- Go back to your API Management instance, then go to APIs, and select your API / Operation for which you want to set up the Managed Identity Authentication.
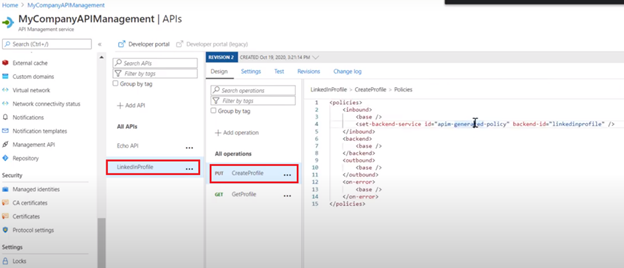
- Put this policy in the inbound policies.
<authentication-managed-identity resource=”” />
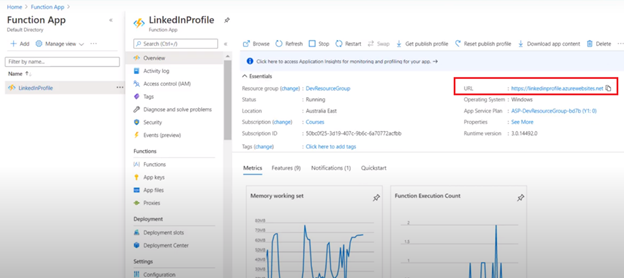
- Go to your Azure Function App and copy the URL. Put it in the resource of the above policy.
- By now your policy should look like the picture below.
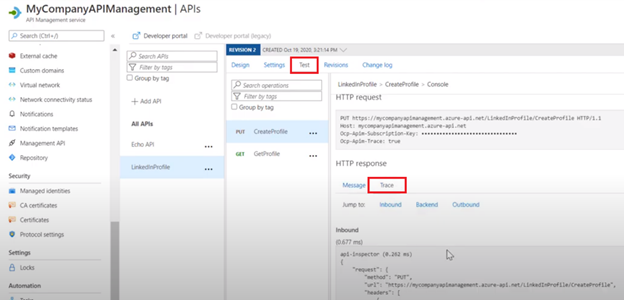
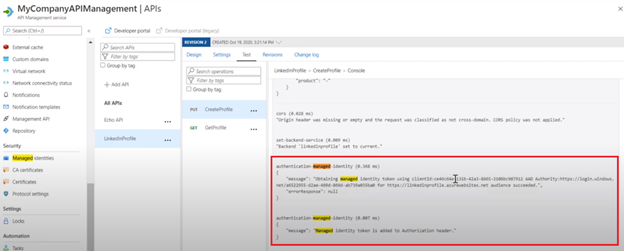
- For validation, go to the test tab in your API Management and send a test request to your API. Then go to the “trace” tab. You should see that Managed Identity authentication has taken place.
- Search for "Managed-identity" in your trace to validate it has been applied.
Was this article helpful?

