- Print
- DarkLight
- PDF
Safeguard Your Data Using Secure Inputs/Outputs in Logic Apps
- Print
- DarkLight
- PDF
A challenge that developers often face when using Azure Logic Apps is how to keep runtime data protected in Run History logs and from support personnel that don’t require that level of information access.
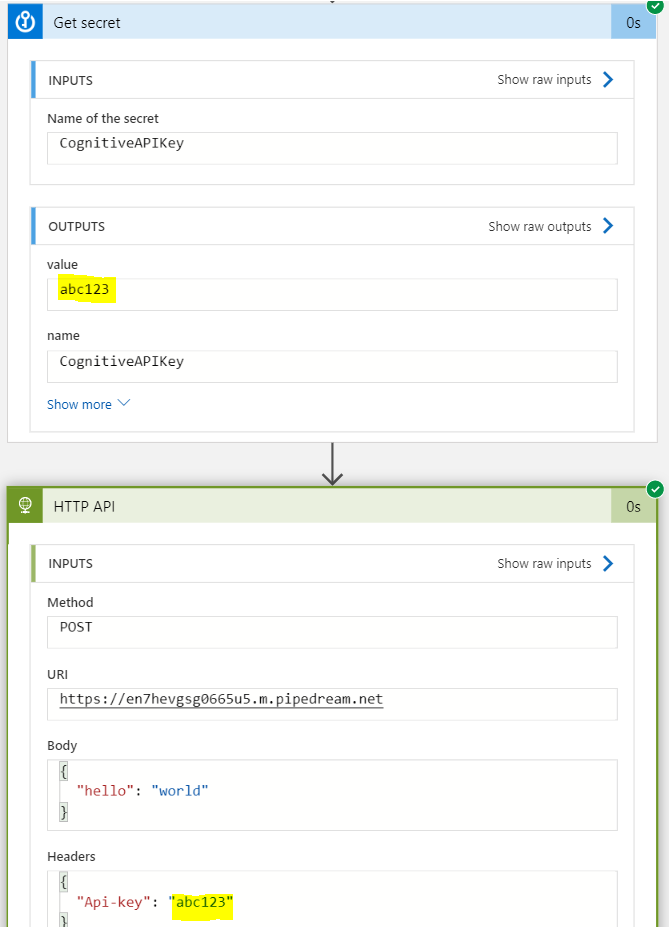
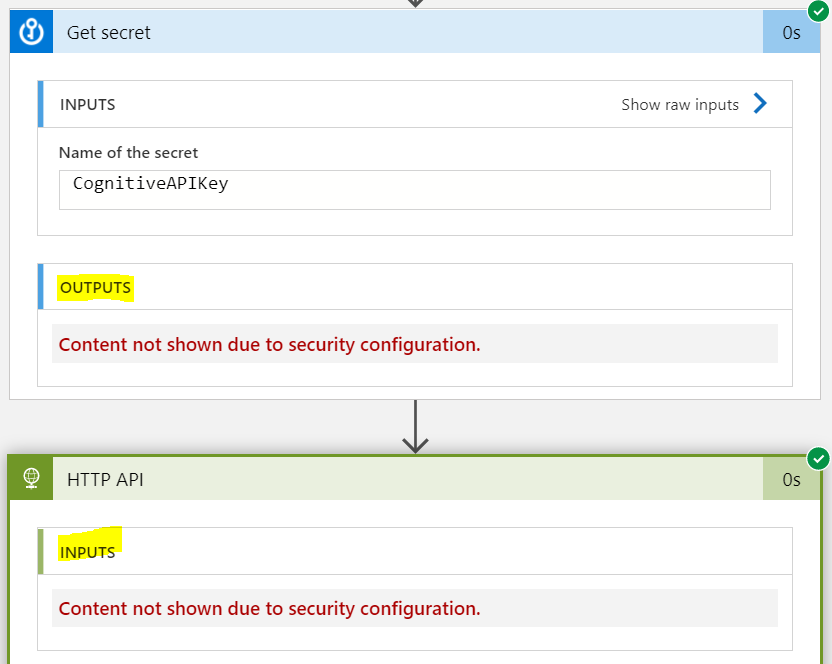
For example, storing secrets, like API keys in Azure Key Value is a valid, and encouraged, approach. That is until you discover that your API key is leaking into your operational logs (Run History) for anyone who has access to those logs to discover. To illustrate this, we can create a secret in Azure Key Vault and then retrieve it via the Azure Key Vault connector. We then pass this key in the header of an HTTP call. After we run our logic app, we can then inspect our Run History and see traces of our key in both our Get secret and HTTP API actions. This is an issue as it de-values the use of Azure Key Vault to keep our secrets safe.
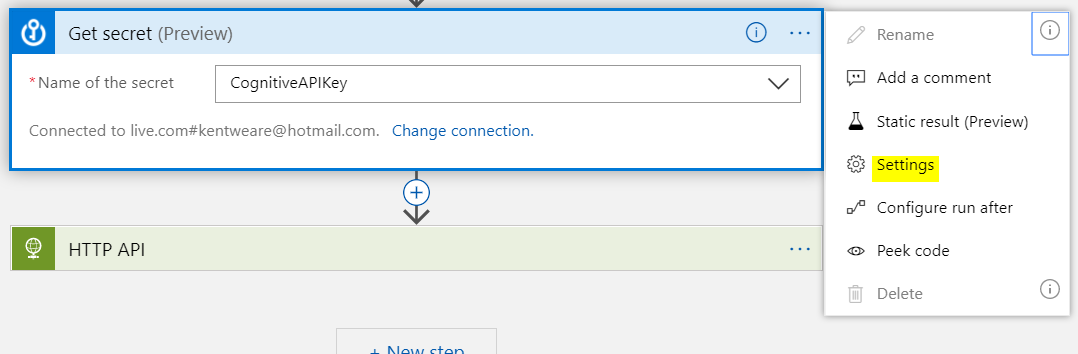
To protect our secrets (or other sensitive data like HR information), we can access Secure Inputs and Secure Outputs configuration from our Settings menu on the action that we want to protect. In our scenario, this will be our Get secret action.
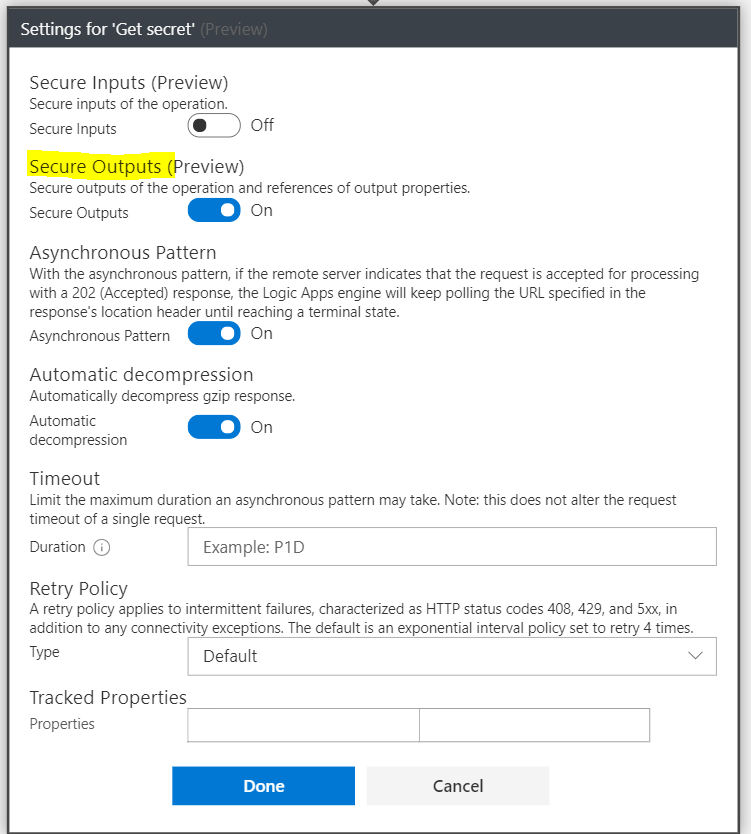
Once we are in our Settings, we have the ability to turn on Secure Inputs and Secure Outputs. With respect to our Azure Key Vault action, we are more concerned with our secret being outputted than any inputs so we will turn On Secure Outputs only.
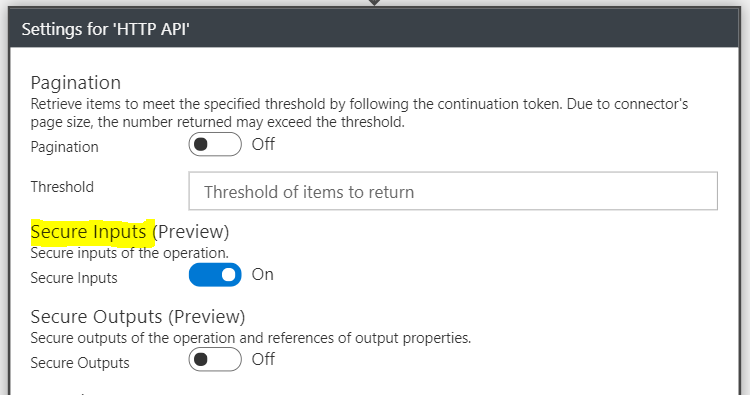
However, because we are using the output from our Key Vault action as an input to our HTTP API, we need to turn On Secure Inputs for that action.
If we run our logic app again, we will see our secret is protected from both the Key Vault action as an output and our HTTP API action as an input.
Conclusion
Secure Inputs and Secure Outputs are relatively new, but provide tremendous value as they allow us to protect sensitive data through both design and run time experiences.


