- Print
- DarkLight
- PDF
Using Microsoft Graph API with Azure Functions
- Print
- DarkLight
- PDF
Microsoft Graph is a set of REST APIs that connects multiple Azure services such as Azure AD, Office 365, and SharePoint and provides a single application for developers to use in custom applications. You can use the Graph API in one of the two modes:
- Delegated permissions: To perform operations for a specific user, such as fetching the calendar, setting automatic replies for the user, etc.
- Application permissions: To perform actions on multiple accounts using the application’s identity.
In this tutorial, we will authorize an Azure Function to use application permission for interacting with the Graph API.
Steps
- Create a file named app-manifest.json which describes the required Graph API permissions that our function needs as follows:
[
{
"resourceAppId": "00000003-0000-0000-c000-000000000000",
"resourceAccess": [
{
"id": "df021288-bdef-4463-88db-98f22de89214",
"type": "Role"
}
]
}
]
In the manifest, the resourceAppId denotes the Id of Microsoft Graph, and the id of the requested access is that for User.ReadAll access. You can use the following commands to get the list of resource app ids and the permissions available for each resource. The schema for the requiredResourceAccess is available on Microsoft documentation:
az ad sp list --query "[].{Name:appDisplayName, Id:appId}" --output table --all
az ad sp show --id <replace with resource app id> --query "appRoles[].{Value:value, Id:id}" --output table
- Open Powershell and use the following Azure CLI command to register an application named graph-api-fx in Azure AD with the following command:
$app = az ad app create --display-name "graph-api-fx" --required-resource-accesses app-manifest.json | ConvertFrom-JSON
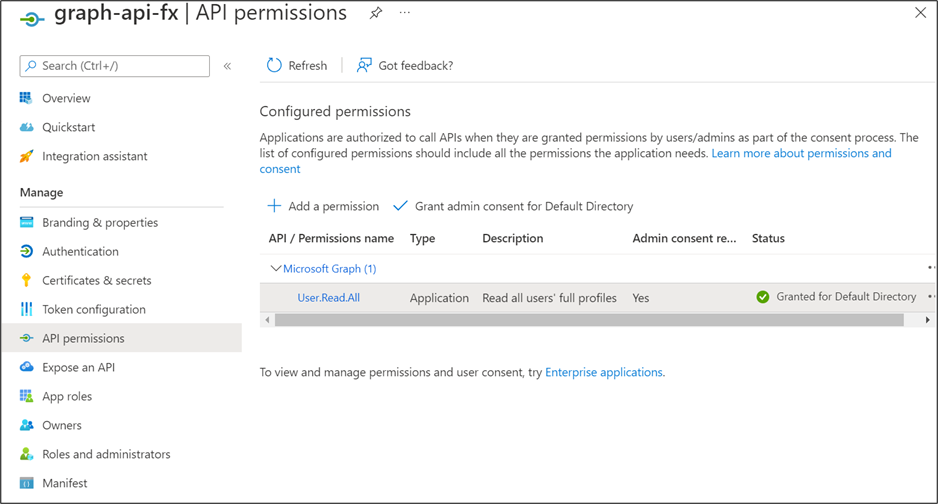
- Some permissions such as User.ReadAll require admin consent. Grant the consent by executing the following command:
az ad app permission admin-consent --id $app.appId
You can check the status of the API permissions in the Azure AD application console as follows:
- Use the following command to generate a secret for your application so that your function can authenticate itself to the Azure AD:
az ad app credential reset --id $app.appId --display-name "Default" | ConvertFrom-Json
Record the password, tenant id, and application id from the command output.
- In your Azure Function (guidance on how to create a C# function), write the following helper function to get an authenticated Graph service client:
private static GraphServiceClient GetAuthenticatedGraphClient()
{
// Read more about scopes: https://docs.microsoft.com/en-us/azure/active-directory/develop/v2-permissions-and-consent
var scopes = new[] { "https://graph.microsoft.com/.default" };
// Values from app registration
var tenantId = "YOUR TENANT ID";
var clientId = "YOUR APP ID";
var clientSecret = "YOUR APP PASSWORD";
var options = new TokenCredentialOptions
{
AuthorityHost = AzureAuthorityHosts.AzurePublicCloud
};
var clientSecretCredential = new ClientSecretCredential(
tenantId, clientId, clientSecret, options);
return new(clientSecretCredential, scopes);
}
- Finally, define your Azure Function that uses the authenticated client to send requests to the Graph API as follows:
[Function(nameof(GetUsers))]
public async Task<HttpResponseData> GetUsers(
[HttpTrigger(AuthorizationLevel.Anonymous, "get")]
HttpRequestData request)
{
var graphClient = GetAuthenticatedGraphClient();
var graphResult = await graphClient.Users
.Request()
.GetAsync();
var response = request.CreateResponse(HttpStatusCode.OK);
await response.WriteAsJsonAsync(graphResult);
return response;
}
Install the Microsoft.Graph and Azure.Identity NuGet packages to the project to add the required dependencies.
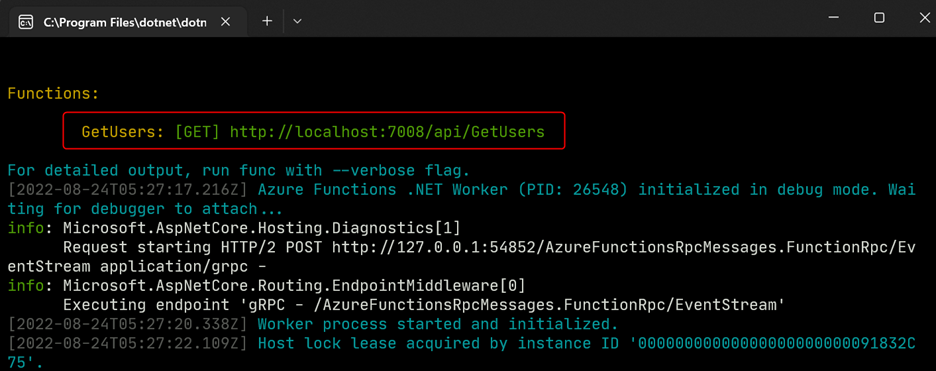
Output
Launch the function on your local system or deploy it to Azure as follows:
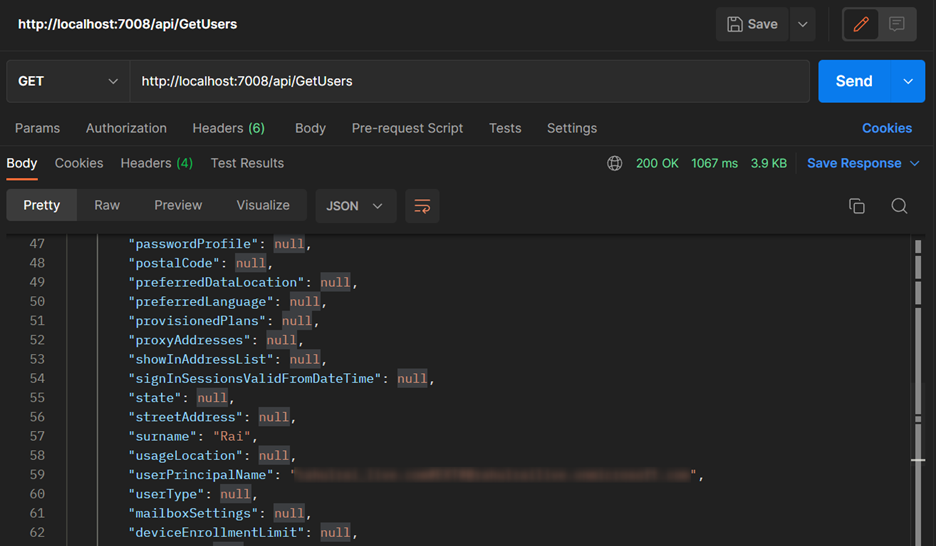
Send a request to the function to get the list of users in your Active Directory as follows: